




The World’s Number 1 Ethical Hacking Certification

Work Anywhere With C|EH- It’s Globally Recognized

A Structured Professional Course for Aspiring Cyber Professionals

Comprehensive Program to Master the 5 Phases of Ethical Hacking

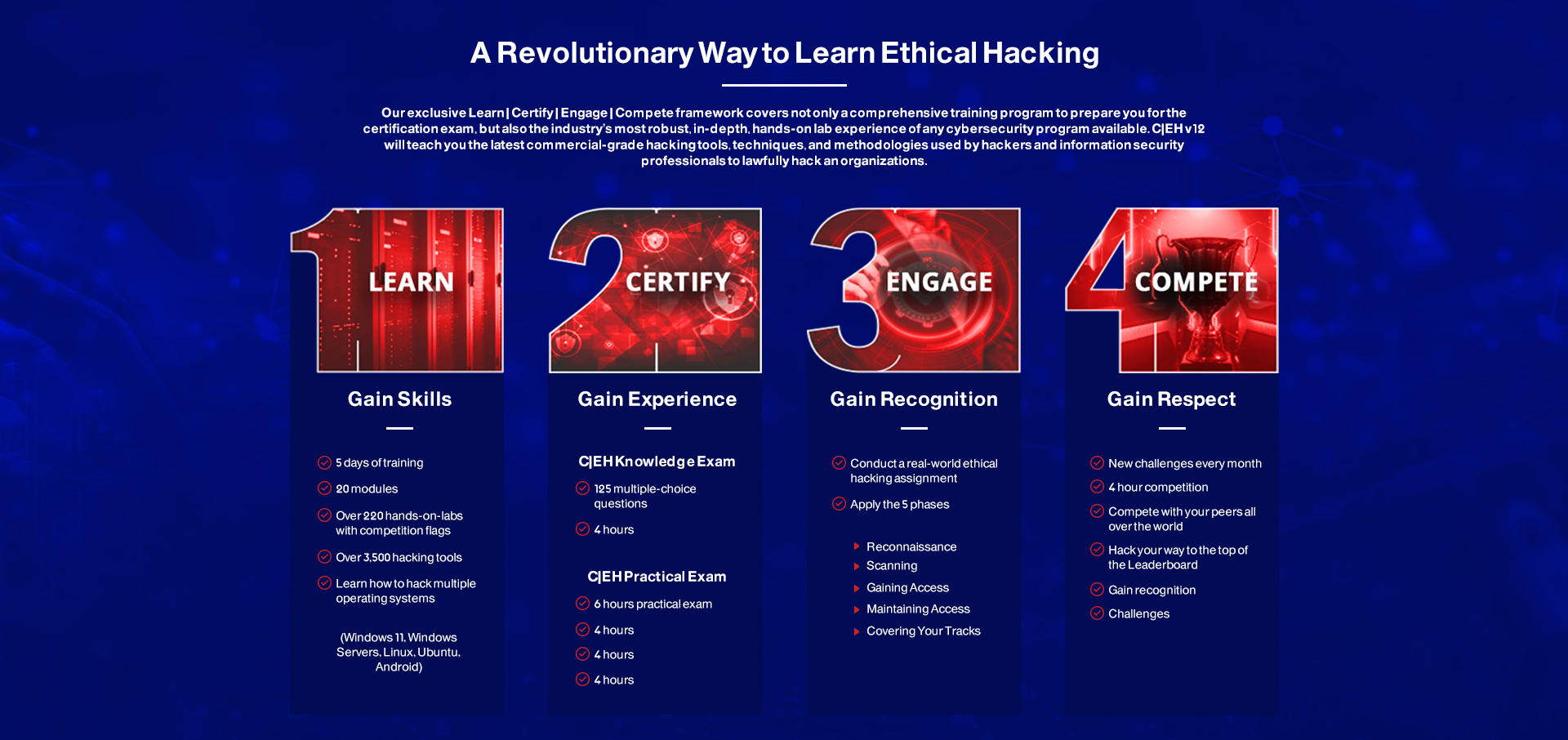
The C|EH exam is a 4-hour exam with 125 multiple-choice questions. This knowledge-based exam will test your skills in Information Security Threats and Attack Vectors, Attack Detection, Attack Prevention, Procedures, Methodologies and more!

C|EH Practical is a 6-hour, rigorous exam that requires you to demonstrate the skills and abilities of ethical hacking techniques such as:

This is the next step to becoming a C|EH Master after you have achieved your C|EH certification. Within C|EH Practical, you have a limited amount of time to complete 20 challenges that test your skills and proficiency in a performance-based cyber range. This exam is NOT a simulation and incorporates a live corporate network of VMs and applications with solutions to uncover vulnerabilities.
Upon Completing the C|EH (Master) program, which consists of C|EH and C|EH (Practical), the C|EH (Master) designation is awarded. C|EH Masters have shown proficiency at a master level in the knowledge, skills, and abilities of ethical hacking with a total 6 hours of testing to prove their competency. Top top 10 performers in both C|EH and C|EH Practical exams are showcased on the C|EH Master Global Ethical Hacking Leaderboard.

20 Modules that help you master the foundations of Ethical Hacking and prepare to challenge the CEH certification exam